Automated User Provisioning / Deprovisioning
VoiceFoundry Agent Desktop supports SCIM provisioning, allowing customers to have their users provisioned and de-provisioned through their corporate access management systems.
The key benefits of enabling automatic user provisioning are:
Increased productivity. You can manage user identities across SaaS applications with a single-user provisioning management interface. This interface has a single set of provisioning policies.
Manage risk. You can increase security by automating changes based on employee status or group memberships that define roles and/or access.
Address compliance and governance. Identity providers commonly support audit logs for every user provisioning request. Requests are executed in both the source and target systems. This enables you to track who has access to applications from a single screen.
Reduce cost. Automatic user provisioning reduces costs by avoiding inefficiencies and human errors associated with manual provisioning. It reduces the need for custom-developed user provisioning solutions, scripts, and audit logs.
To set up user provisioning, your identity management system needs to support automated provisioning and have any applicable licensing from your vendor.
AzureAD supports automated user provisioning with all Azure Active Directory editions however you can only use Security Groups wtih P1 & P2 licenced plans.
Okta supports automated user provisioning however you need to have a licence for Lifecycle Management.
VoiceFoundry recommends using security groups with SCIM provisioning where possible, as when using this configuration, a security profile will be created in Agent Desktop (and subsequently Amazon Connect) with the name of the security group, allowing administrators with an easy reference to know what permissions users have.
VoiceFoundry has tested SCIM with AzureAD and Okta. Whilst many other plaforms support the SCIM standard, we do not provide support for other identity provider tools. VoiceFoundry recommends customers speak with their Information Technology department to get assistance with this configuration.
Agent Desktop Configuration
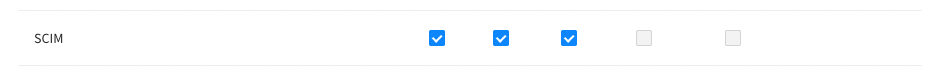
To be able to configure SCIM provisioning, the administrator must have enabled SCIM permission in their security profile. Users do not need this permission and should not be granted it.
To enable SCIM:
Go to Security Profiles.
Select the appropriate security profile to which the administrator belongs.
Check SCIM checkboxes under Agent Desktop Configuration.
Generate integration token
During your SCIM configuration, you will require the System API BaseURL and Token. Your Systems API BaseURL will be provided by the VoiceFoundry Cloud team. If you do not have this, please email cloudops@voicefoundry.cloud requesting your System API BaseURL.
Once you have the base URL for your tenant, follow the below steps to generate a Token:
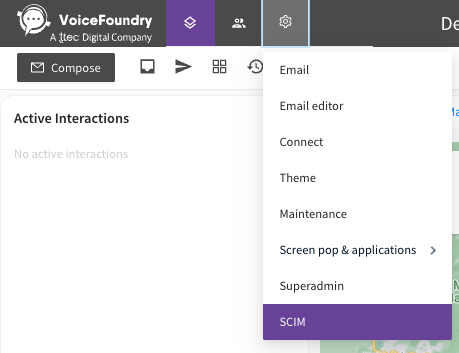
Under the configuration menu, select SCIM
Select a default routing profile and security profile and click Save. Default routing profiles and security profiles are used if you do not configure those values to be passed in provisioning attributes.
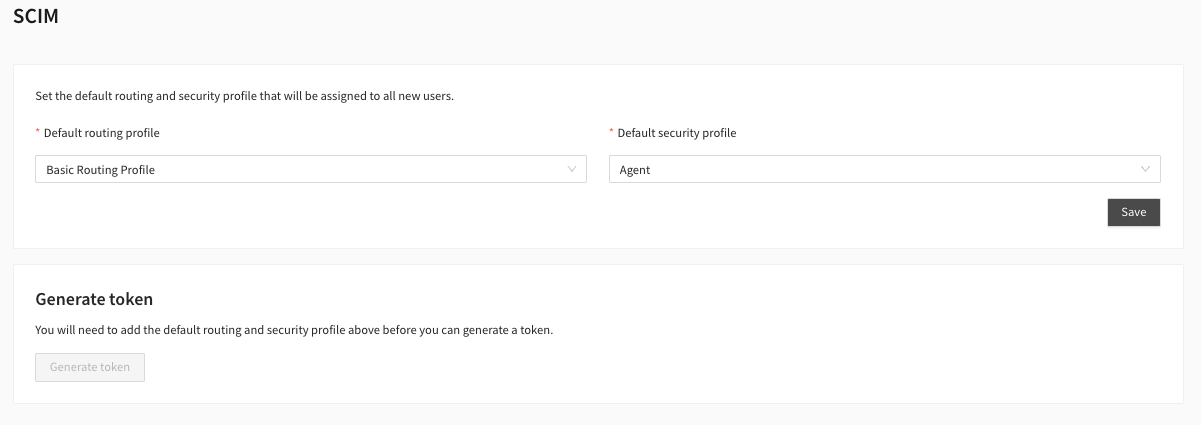
Once you have saved your default configuration, click the “Generate token“ button to generate a token that will be copied to the clipboard. This token will be used later in the SCIM integration with the provider of your choice.
VoiceFoundry Cloud team must activate SCIM in your tenant before you are able to generate a token for security purposes.

SCIM Attributes
The below user attributes must be passed to the SCIM endpoint.
User Attributes
Attribute | Value |
|---|---|
| This should be the value which is passed in the SAML login request from the value “RoleSessionName”, commonly the users email address. This is case sensitive and must match exactly |
| The users given name (first name) |
| The users family name (last name) |
| The users routing profile |
| The name of the security profile that should be assigned to a user, or the security group name. |
| Pass as a boolean value ('true' or 'false' |
Group Attributes
Attribute | Value |
|---|---|
displayName | The name of the security group. This will create a security profile within Agent Desktop & Amazon Connect. |
Configuration Guides
VoiceFoundry CloudOps team can provide configuration guides for AzureAD and Okta. We do not provide configuration advice for other identity providers.
